BroadWeb
Essential Eight Maturity Model
What Is Essential Eight Maturity Model (E8MM)?
The Essential Eight Maturity Model (E8MM) is a framework that helps organizations assess and improve their implementation of the Essential Eight, a set of eight cybersecurity mitigation strategies that are proven to be effective against a wide range of cyber threats. The E8MM is based on the Australian Signals Directorate’s (ASD) experience in producing cyber threat intelligence, responding to cybersecurity incidents, conducting penetration testing, and assisting organizations to implement the Essential Eight.
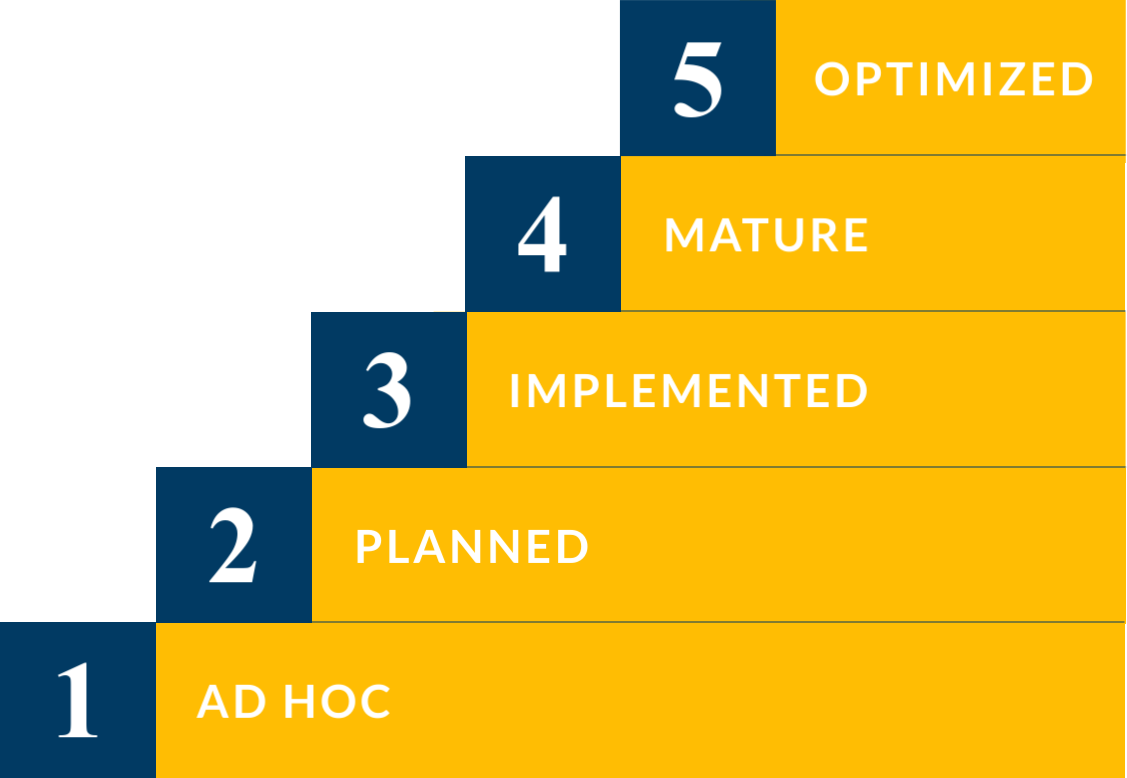
The E8MM defines five maturity levels for each of the Essential Eight mitigation strategies:
- Level 1: Ad hoc – The organization has not implemented the mitigation strategy or has implemented it in an ad hoc manner.
- Level 2: Planned – The organization has a plan to implement the mitigation strategy but has not yet fully implemented it.
- Level 3: Implemented – The organization has implemented the mitigation strategy but it is not fully mature.
- Level 4: Mature – The organization has implemented the mitigation strategy and it is mature.
- Level 5: Optimized – The organization has optimized the mitigation strategy and it is continually improving it.
What Can Essential Eight Maturity Model (E8MM) Be Used For?
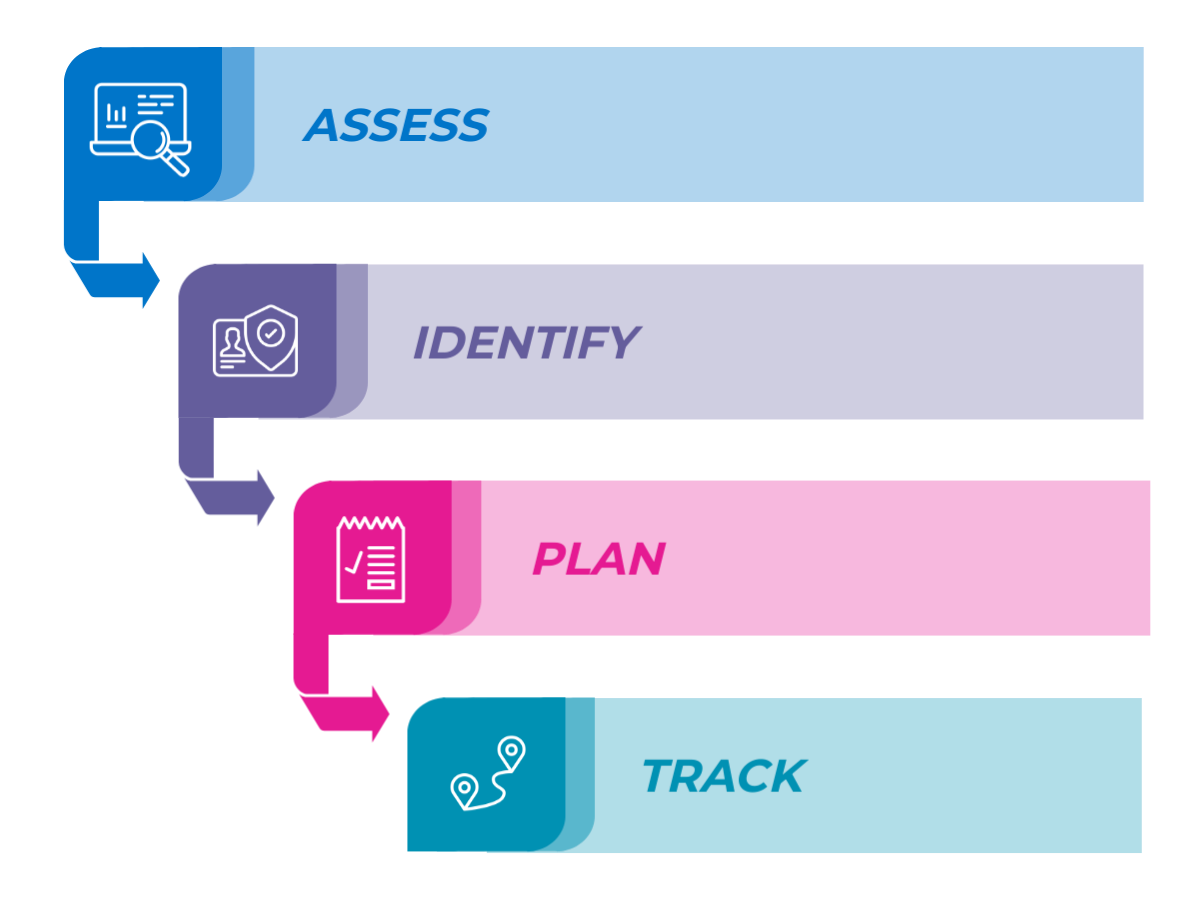
The E8MM can be used to:
- Assess the current maturity level of an organization’s implementation of the Essential Eight.
- Identify areas where the organization can improve its implementation of the Essential Eight.
- Develop a plan to improve the organization’s implementation of the Essential Eight.
- Track the organization’s progress in improving its implementation of the Essential Eight.
The E8MM is a valuable tool for organizations that want to improve their cybersecurity posture and reduce their risk of cyberattacks.
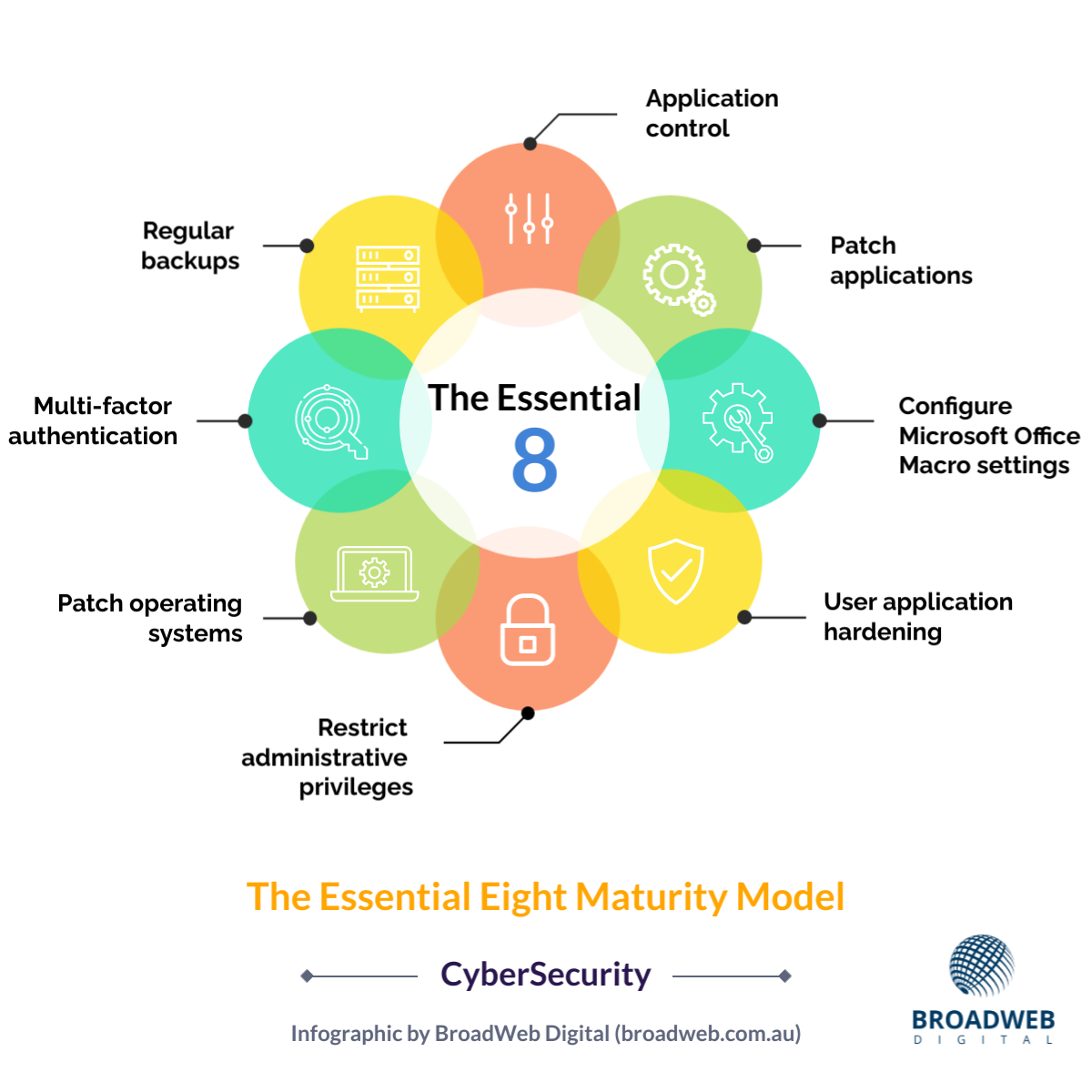
What Are the 8 Mitigation Strategies That Make up Essential Eight Maturity Model (E8MM)?
Here are the eight mitigation strategies that make up the Essential Eight:
- Application control: This strategy involves controlling which applications can run on an organization’s systems. This helps to prevent malicious applications from being installed and executed.
- Patch applications: This strategy involves regularly patching software vulnerabilities. This helps to close security holes that attackers can exploit to gain access to systems.
- Configure Microsoft Office macro settings: This strategy involves configuring Microsoft Office macros to be disabled by default. This helps to prevent malicious macros from being executed.
- User application hardening: This strategy involves configuring user applications to make them more resistant to attacks. This can include disabling unnecessary features, enabling security settings, and using application whitelisting.
- Restrict administrative privileges: This strategy involves restricting administrative privileges to only those users who need them. This helps to limit the damage that can be caused if an account is compromised.
- Patch operating systems: This strategy involves regularly patching operating system vulnerabilities. This helps to close security holes that attackers can exploit to gain access to systems.
- Multi-factor authentication: This strategy involves requiring users to provide multiple pieces of evidence to authenticate their identities. This makes it more difficult for attackers to gain access to accounts.
- Regular backups: This strategy involves regularly backing up data so that it can be restored in the event of a cyberattack.